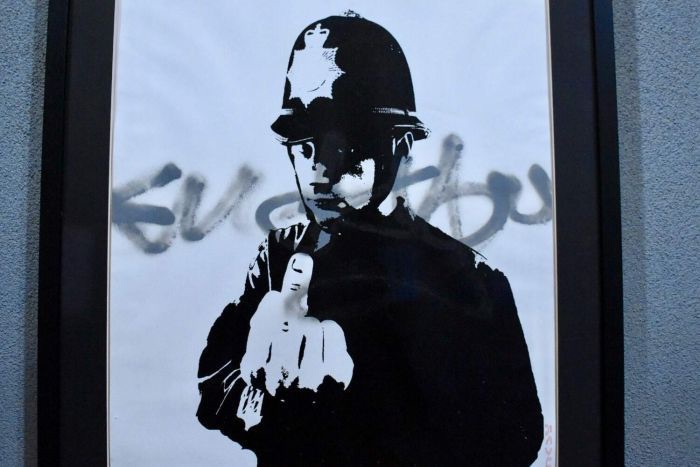
"Justice System" Based on Government Coercion & Violence: Do You "Consent" to "Near Perfect Surveillance of All Your Movements" [ankle monitoring] or Want to be Locked Up Pending Trial?
/From [HERE] Our phones are constantly searching for the greatest connection, updating our location, and often connect to multiple cell towers on any given day, divulging our whereabouts to service providers with relative ease. In recent years, the accuracy of this method to pinpoint a person’s current and past location has increased significantly. And given that there are more cell phone accounts in America than there are people in the country, wireless providers are the gatekeepers to a wealth of stored information about our daily movements.
Privacy advocates and those legitimately concerned with the attendant constraints of Big Brother government have looked to the U.S. Supreme Court’s ruling in Carpenter v. United States as a major victory, as it settles several questions about the protections that citizens have when the government seeks to use third parties to access personal information such as location. The United States Supreme Court’s position on the essentialness of cell phones to everyday life and Americans’ expectation that the government is not tracking them at every moment, in many ways builds upon its decision in Riley v. California. In Riley, the Court ruled that the contents of a cell phone found on a person may not be searched as a part of placing that individual under arrest, given the heavy expectations of privacy citizens have in the information that may be retrieved from a cell phone (in the case of David Riley, contacts and photos). Location data, in particular, can reveal intimate details about a person’s life, from visits to medical clinics, to attendance at community and political group gatherings, to trips to the liquor store.
It is hard to imagine that Timothy Carpenter, upon receiving a hundred and sixteen-year prison sentence, would have found the humor that some have found in the irony of his alleged string of store robberies involving cell phone theft, and law enforcement using cell phone technology to ultimately identify him. The Court in Carpenter, however, found this acquisition by the government of cell-site records from his wireless carriers was a Fourth Amendment search, requiring a warrant based upon probable cause, and granted his appeal of the conviction and sentence. Before Carpenter was identified by law enforcement as involved in the robberies of Radio Shack and T-Mobile stores in Michigan and Ohio, his cell phone number was found in the call log of another suspect. Federal prosecutors then made a request, without a warrant, to several wireless carriers and received over four months’ worth of cell-site records with location data. Law enforcement agents were able to connect Carpenter to the location of the robberies through triangulation methods that estimate a cell phone’s location within a cell site.
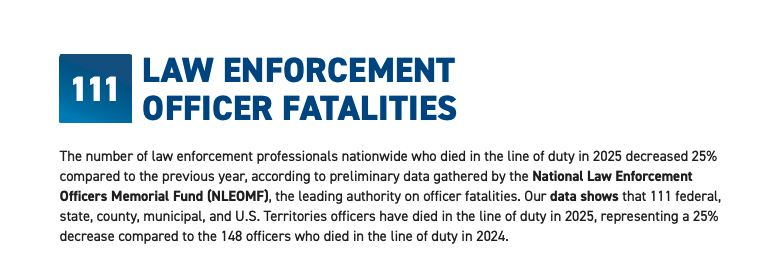
While the significance of this case cannot be overstated, there are many questions left unanswered by Carpenter concerning other methods of state surveillance in both corrections and policing. Interestingly, in articulating the concern in the case, the Court noted that “when the Government tracks the location of a cell phone it achieves near perfect surveillance, as if it had attached an ankle monitor to the phone’s user.” Some may be surprised to discover that all fifty states do in fact attach electronic ankle monitors on hundreds of thousands of people every year as a condition of pretrial and post-conviction release. In a report on the expansion of electronic surveillance, the Pew Charitable Trust notes that the use of electronic surveillance devices in the criminal justice system rose 140% between 2005 and 2015. During this same period, GEO Group and CoreCivic (formerly Corrections Corporation of America), private prison corporations, invested billions of dollars in ankle monitor surveillance technology.
I highlight, in a recent law review article, how these correctional surveillance technologies are even used frequently on minors, in ways that compromise the rehabilitative aim of juvenile court. This form of surveillance has also been widely used in the immigration system through programs under innocuous titles such as “Family Case Management.” During the recent controversy over the policy of separating migrant parents from their children, such surveillance programming was suggested as a reasonable solution, at a minimal cost.
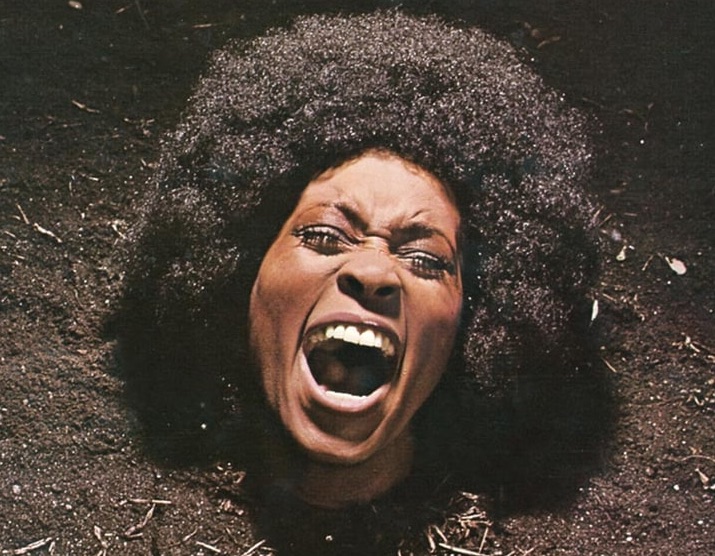
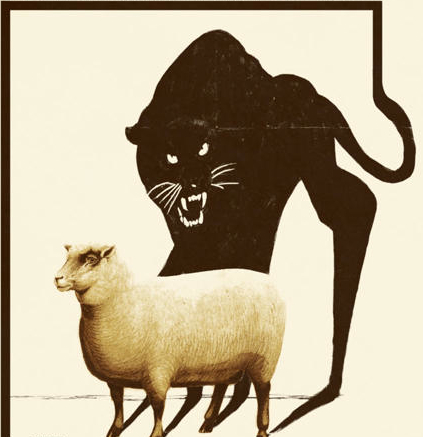
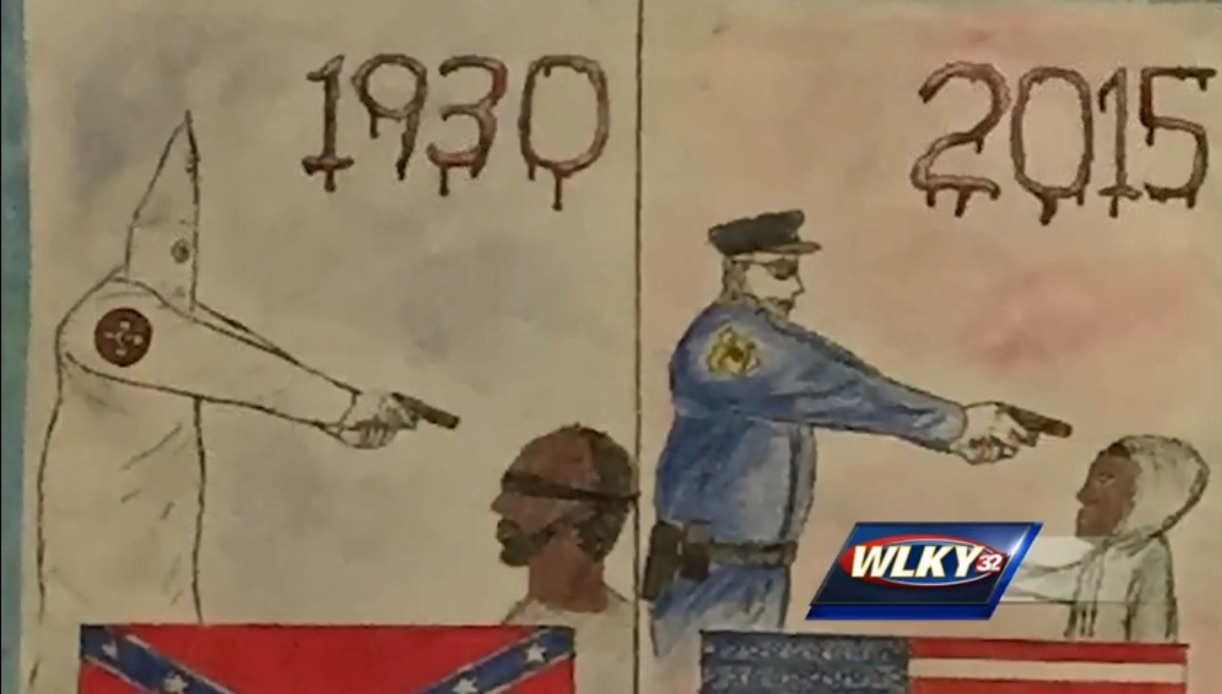
The potential for dehumanization that comes with locking tracking devices on adults and their children, not only presents psychological harms from stigma and shame, but may also act to widen the overcriminalization net, entrenching a marginalized, subordinated class of individuals with digital scarlet letters. We are only beginning to examine the deep social costs of this expanded carceral reality, best understood as e-carceration. But what we already know is that its burden falls heaviest on poor communities of color.
Thus, one of the questions that is not addressed by Carpenter is whether this ruling opens the door for new interpretations on how the location data collected by correctional surveillance technology, such as ankle monitors, should be protected. In Grady v. North Carolina, in a case involving the use of GPS ankle monitors on sex offenders, the Supreme Court decided that the state “conducts a [Fourth Amendment] search when it attaches a device to a person’s body, without consent, for the purpose of tracking that individual’s movements.” Although at pretrial and post-conviction release individuals voluntarily consent to be monitored, the Court in Carpenter noted that when it comes to the location data that cell phones provide, the “voluntary exposure” rationale does not hold up. One could ask whether those on ankle monitors, which are increasingly supervised by private for-profit probation companies, voluntarily expose their location data when the option presented is imprisonment or “near perfect surveillance.” And like Timothy Carpenter, individuals on ankle monitors risk having their location data used to place them at the scenes of crimes, without the need for a search warrant.
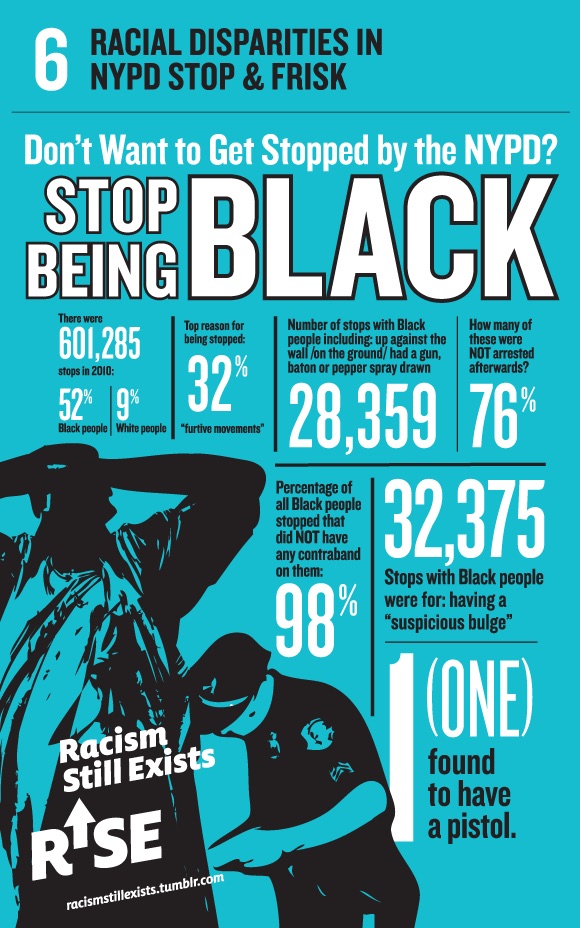
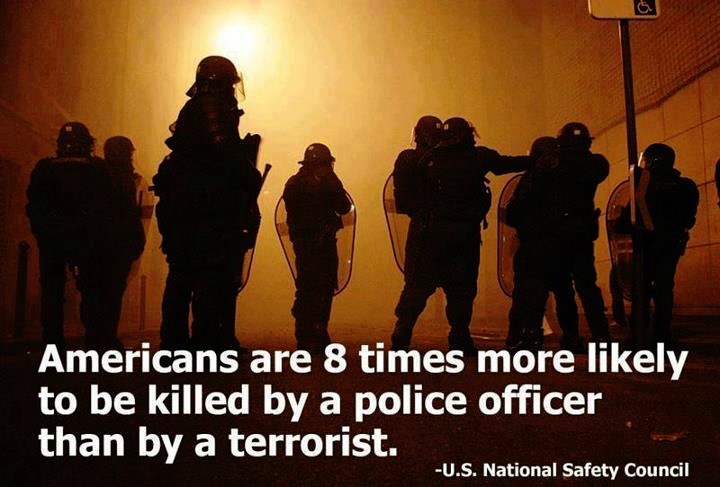
Questions also remain for the extent of constitutional protections that may be afforded against newer forms of police surveillance technology. The type of location data used to convict Timothy Carpenter has been used in criminal cases for at least twenty years. In the now infamous murder case of Adnan Syed for the 1999 killing of Hae Min Lee, which is chronicled on the Serial podcast, cell site data garnered by nearby cell towers was a significant piece of evidence use by prosecutors in the February 2000 trial. The Supreme Court has been notoriously slow in catching up to the speed of advancing surveillance technology in policing. In just the past few years police departments have acquired highly sophisticated modes of surveillance such as facial recognition and pre-crime software technology that makes algorithm-generated predictions on who is likely to commit crime and where. These technologies have already received considerable criticism for their inherent racial biases and disproportionate impacts on communities of color.
If the Supreme Court in 2018 believes that the arguably rudimentary technology of ankle monitoring is near perfect, then the current law enforcement foray into the wildly powerful, yet flawed, surveillance measures of the future, may present frightening possibilities for limiting privacy and maximizing social control of vulnerable communities. And given the pace of the jurisprudence in this area, these fundamental concerns are not likely to reach the highest court for quite some time.
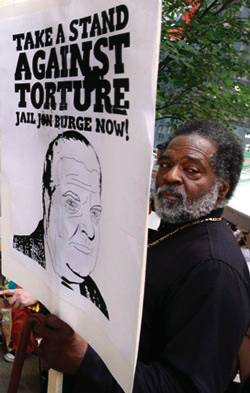
Most advocates fearing the encroaching surveillance state recognize that courts may not be the best route for pushing back against current police and correctional surveillance measures. The recent Supreme Court nomination, with Brett Kavaughn’s purported stance on privacy, will likely only lessen any confidence for increasing protections through litigation. Instead, advocates have focused on building local and national movements for change. For example, in corrections, the Center for Media Justice launched the “Challenging E-Carceration” project to contest the use of electronic ankle monitoring in the criminal justice and immigration system as a human rights issue, and released a set of guidelines to support advocates and policymakers. In policing, the American Civil Liberties Union introduced the Community Control Over Police Surveillance (CCOPS) effort. The campaign’s principal objective is to pass CCOPS laws that ensure the elevation of residents’ voice and input into law enforcement decisions about the adoption and deployment of surveillance technologies. Even corporate shareholders have organized to raise concerns over surveillance technologies.
These new debates and movements reveal that we are only at the tip of the enhanced state surveillance iceberg. The toughest battles in balancing the risks and rewards of such technologies lie ahead. Perhaps the most important question left unresolved by Carpenter is not how we should use surveillance technologies, but rather whether some forms of surveillance technology should be used at all.